Advertisement|Remove ads.
$280M Drift Protocol Hack Mirrors $1.5B Bybit Breach – Ledger CTO Says Signers ‘Unknowingly’ Authorized Drain

- "According to Ledger CTO Charles Guillmet, the attackers likely compromised the multisignature approval process to authorize malicious transactions.
- He said the signers may have unknowingly approved fraudulent transactions, believing them to be legitimate.
- Drift’s native token fell to a record low following the incident before partially recovering.
Ledger chief technology officer (CTO) Charles Guillemet on Thursday compared the Drift Protocol hack to the $1.5 Bybit exploit last year, widely attributed to North Korean hackers.
“The pattern is becoming familiar: patient, sophisticated supply-chain-level compromise targeting the human and operational layer, not the smart contracts themselves,” he wrote in a post on X, calling the Drift Protocol hack “the biggest hack of 2026” and “one of the largest ever on the Solana blockchain.”
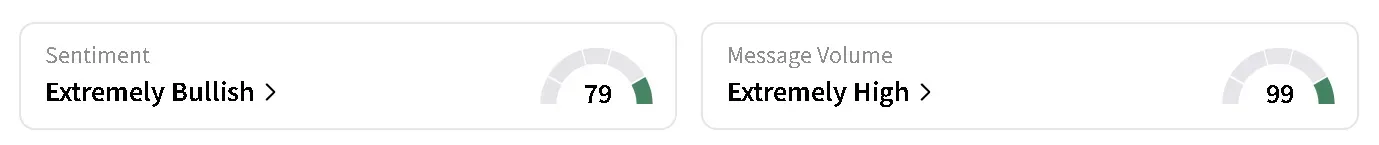
DRIFT’s price tumbled to a record low of $0.038 after the incident, before paring its losses. The altcoin was still down 40% in the last 24 hours at the time of writing, trading at around $0.043. Retail sentiment around DRIFT’s token on Stocktwits turned ‘extremely bullish’ from ‘neutral’ over the past day, rising to the highest level seen this year. Meanwhile, retail chatter rose to ‘extremely high’ from ‘high’ levels.
Drift Protocol Hack Mirrors Bybit Attack Pattern
Guillemet said the Drift incident was not caused by a flaw in smart contracts, but by a breakdown in operational security. According to him, attackers appeared to have gained control over the protocol’s multisignature process, enabling them to authorize malicious transactions and drain funds.
The method closely mirrors the Bybit attack, which also relied on gaining trusted access rather than exploiting code. In both cases, the attack vector shifted away from smart contract risk toward the security of people and processes managing access.
"The signers may have believed they were signing a legitimate operation while unknowingly authorizing the drain." – Charles Guillemet, Chief Technology Officer, Ledger
Security Breakdown Occurred Outside Smart Contracts
Guillemet said that Drift’s smart contracts remained intact during the exploit. He noted that instead of exploiting bugs, attackers are increasingly targeting operational layers — including device security, key management, and approval workflows.
Guillemet said protocols need stronger endpoint protection and more secure signing mechanisms, including hardware-backed systems that reduce the risk of compromised approvals. Other calls were similarly echoed for improved security standards across the industry.
Drift said all protocol functions have been frozen, and the multisig has now been updated to remove the compromised wallet. It added that it is working with exchanges, cross-chain bridges, and law enforcement agencies to trace and potentially recover the stolen funds.
Read also: Bitcoin Falls Below $67,000 After Oil Spikes, Trump's Iran Warning Rattles Risk Assets
For updates and corrections, email newsroom[at]stocktwits[dot]com.

/filters:format(webp)https://news.stocktwits-cdn.com/large_Getty_Images_129268875_jpg_65473aef80.webp)
/filters:format(webp)https://news.stocktwits-cdn.com/Aashika_Suresh_Profile_Picture_jpg_2acd6f446c.webp)
/filters:format(webp)https://news.stocktwits-cdn.com/large_Getty_Images_2267825783_jpg_1b90bf709b.webp)
/filters:format(webp)https://st-everywhere-cms-prod.s3.us-east-1.amazonaws.com/unnamed_jpg_9dff551b50.webp)
/filters:format(webp)https://st-everywhere-cms-prod.s3.us-east-1.amazonaws.com/large_sealsq_stock_market_representative_resized_b05435011f.jpg)
/filters:format(webp)https://st-everywhere-cms-prod.s3.us-east-1.amazonaws.com/large_chewy_5s_Gjkp_N_Dm_LI_unsplash_1_a1dcde4143.jpg)
/filters:format(webp)https://news.stocktwits-cdn.com/1707726834303_jpg_11f20a9aa9.webp)
/filters:format(webp)https://news.stocktwits-cdn.com/large_Getty_Images_2154180384_jpg_33ad41eb60.webp)
/filters:format(webp)https://news.stocktwits-cdn.com/Getty_Images_2227552516_jpg_55b091826e.webp)